Technology
A Self-Organizing, Cryptographically Verifiable Live Streaming Network
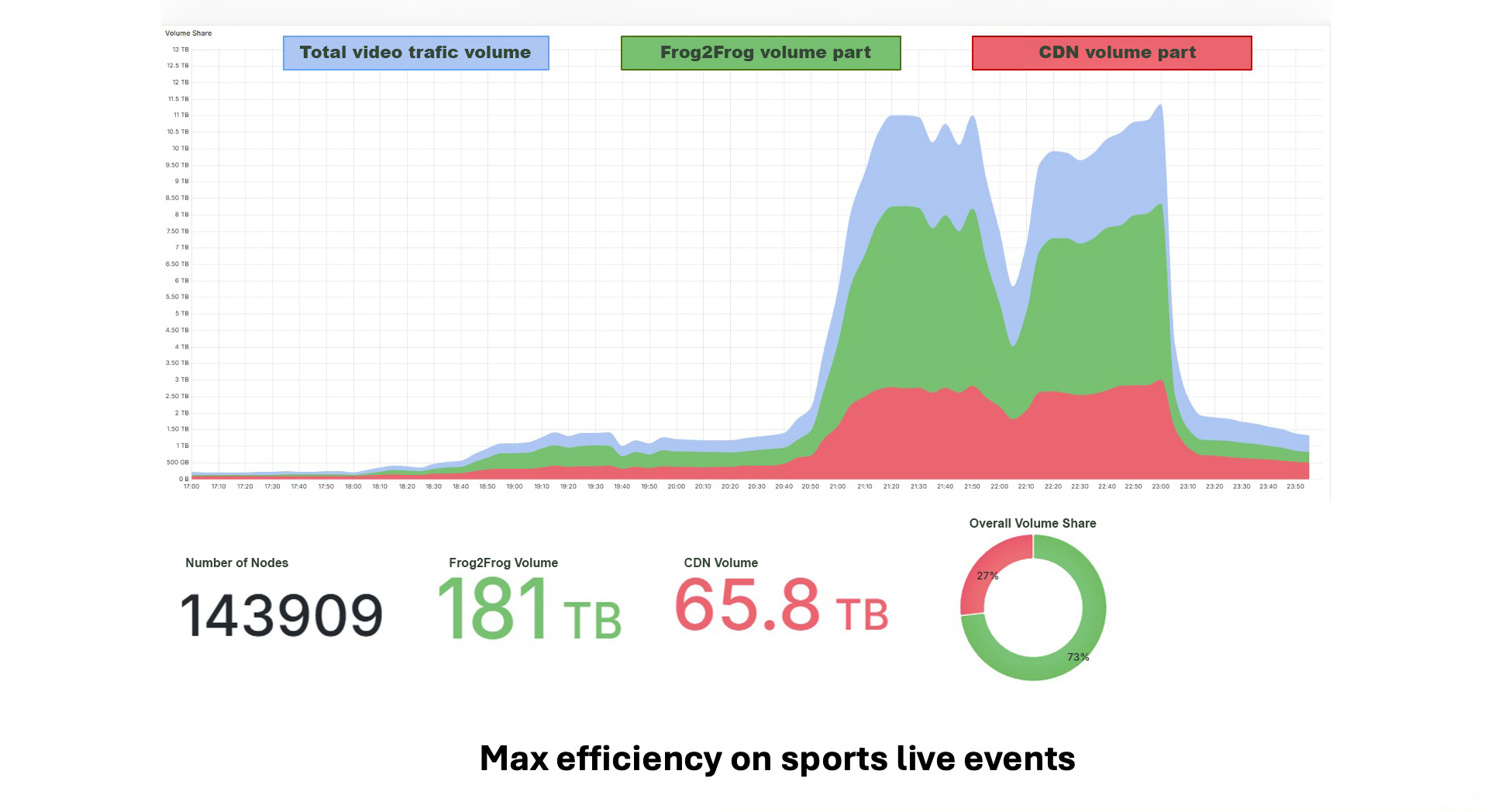
Frog2Frog is a hybrid P2P-CDN delivery architecture designed to transform large-scale live streaming from an infrastructure-scaling problem into a self-organizing distributed system. It combines structured peer-to-peer overlays, AI-driven topology optimization, pairing-based cryptography to deliver broadcast-grade Quality of Experience with deterministic security guarantees.
What the System Is
Frog2Frog is a distributed overlay network built on top of existing CDN infrastructure.
At its core:
- The CDN remains the origin, fallback, and authorization anchor
- Each viewer device runs a lightweight Frog2Frog Agent
- Devices consuming the same stream form a dynamic swarm
A swarm is a content-scoped group of devices that exchange video segments directly with one another. It functions as a temporary, distributed micro-CDN dedicated to a specific live stream.
The system is therefore hybrid:
- Centralized control and authorization
- Decentralized execution and distribution
How the Network Emerges
Network formation is deterministic and content-driven.
When a stream starts:
- The node computes a unique identifier of CDN URL, tokens, or SSAI mutations.
- Node discovery proceeds via gossip-based neighbor exchange.
- Devices consuming the same identifier converge into the same swarm.
No central registry is required after bootstrap.
Swarm membership evolves organically and self-heals under churn.
As audience grows:
- Each new participant adds both demand and upload capacity.
- Aggregate delivery capacity increases proportionally.
Scalability becomes an emergent property of the network.
How It Secures Itself
Security is embedded directly into the overlay.
Each node derives its identity from a blockchain-grade pairing-based key pair.
PeerId is cryptographically bound to its public key, enabling:
- Compact signature aggregation
- Efficient multi-party verification
- Strong Sybil resistance
To preserve CDN authorization guarantees, Frog2Frog relies on server-side watermarking and session-aware token management to control and trace content access.
How It Optimizes Itself
Frog2Frog continuously reorganizes its overlay.
Peer selection is AI-driven and based on real-time metrics:
- RTT
- Throughput
- Bandwidth estimation
- Reliability scoring
- Churn indicators ...
A learning-based model computes optimal neighbor sets to maximize aggregate throughput and minimize congestion.
Topology refinement occurs through distributed swap consensus:
- Nodes propose local rewiring.
- Gains are evaluated.
- Atomic transitions are committed without central coordination.
Segment delivery is opportunistic:
- For each segment, nodes are ranked dynamically.
- The best source, node or CDN, is selected in real time.
- Instant fallback prevents playback degradation.
The network learns and stabilizes itself continuously.
How It Is Operated
Although execution is decentralized, operations remain centralized and deterministic.
A multi-channel telemetry architecture streams:
- Debug metrics
- Billing attribution
- Delivery verification
- Network health indicators
Operators access real-time dashboards showing:
- Swarm topology evolution
- Offload ratios
- Reliability anomalies
Remote configuration allows dynamic tuning of:
- Peer selection thresholds
- Verification sampling rates
- Transport preferences
- Feature activation
No redeployment is required for parameter changes.
How It Is Deployed
Frog2Frog is powered by a unified core engine deployed across:
- Linux
- Android
- iOS / macOS
- WebAssembly (browser runtime)
Two integration models are supported:
HTTP Proxy Mode
- Transparent interception
- No player modification required
Custom Segment Loader API
- Programmatic control
- Advanced scheduling and retry strategies
Both modes preserve full compatibility with cryptographic verification and watermark workflows.
